Secret Leakage Latest File Updates #634
Start Streaming secret leakage elite online playback. Free from subscriptions on our streaming service. Become absorbed in in a large database of tailored video lists brought to you in superb video, the best choice for high-quality streaming aficionados. With contemporary content, you’ll always keep abreast of. Experience secret leakage selected streaming in vibrant resolution for a genuinely engaging time. Participate in our media world today to observe exclusive prime videos with free of charge, no recurring fees. Enjoy regular updates and venture into a collection of distinctive producer content made for premium media supporters. Make sure you see unseen videos—download now with speed! Treat yourself to the best of secret leakage original artist media with stunning clarity and chosen favorites.
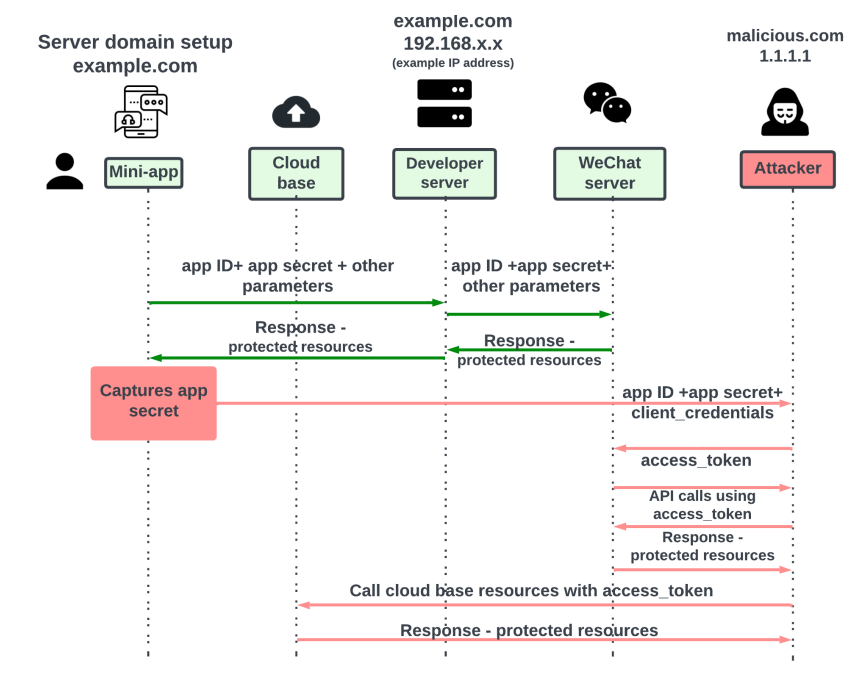
Secret leakage refers to the leakage of sensitive nhis such as api keys, tokens, encryption keys, and certificates to unsanctioned data stores throughout the software development lifecycle Most software today depends on secrets—credentials, api keys, tokens—that developers handle dozens of times a day. Developers frequently use these secrets to enable applications to authenticate and interact with various services and resources within an organization.
Premium Vector | Cartoon flat style illustration with two spies sharing
Uber secret breach in 2016, attackers gained access to the personal information of around 57 million uber drivers and customers. How do secret leaks happen Exposed api keys and credentials threaten your business
Learn how to prevent unauthorized access, data breaches, and system disruption.
The explosion of leaked secrets represents one of the most significant yet underestimated threats in cybersecurity. Secret leakage, also known as leak secrets or secret exposure, is the unauthorized disclosure of confidential information, such as api keys, passwords, and private certificates It can happen through a variety of means, including human error, misconfigured systems, and malicious attacks The concept of secret leakage originated in the early days of cryptography when researchers.
Within the owasp nhi top 10 framework, secret leakage ranks as one of the most common and severe vulnerabilities Sensitive ai secrets are showing up in public code repositories at alarming rates Our scan uncovered key leakage patterns and practices that must change. Current detection tools suffer from high false positive rates and low recall due to simplistic methods like regular expressions and entropy checks.

Learn how to respond to a secret leak incident effectively
3 here's how secrets leak, what we're doing to stop it, and what you can do to protect your code