Leak Site Content Update Files & Photos #886
Claim Your Access leak site world-class live feed. Subscription-free on our video archive. Get lost in in a large database of featured videos ready to stream in premium quality, a dream come true for first-class streaming aficionados. With recent uploads, you’ll always be in the know. Discover leak site preferred streaming in retina quality for a highly fascinating experience. Register for our media center today to experience content you won't find anywhere else with totally complimentary, subscription not necessary. Experience new uploads regularly and investigate a universe of indie creator works built for exclusive media addicts. Make sure you see special videos—start your fast download! Enjoy the finest of leak site special maker videos with impeccable sharpness and staff picks.
Learn how dark web leak sites occur, how cybercriminals expose stolen data, and the best ransomware prevention practices to protect sensitive information. Today, 21 december 2018, wikileaks publishes a searchable database of more than 16,000 procurement requests posted by united states embassies around the world. The dark web hub is an online resource for those investigating the dark web
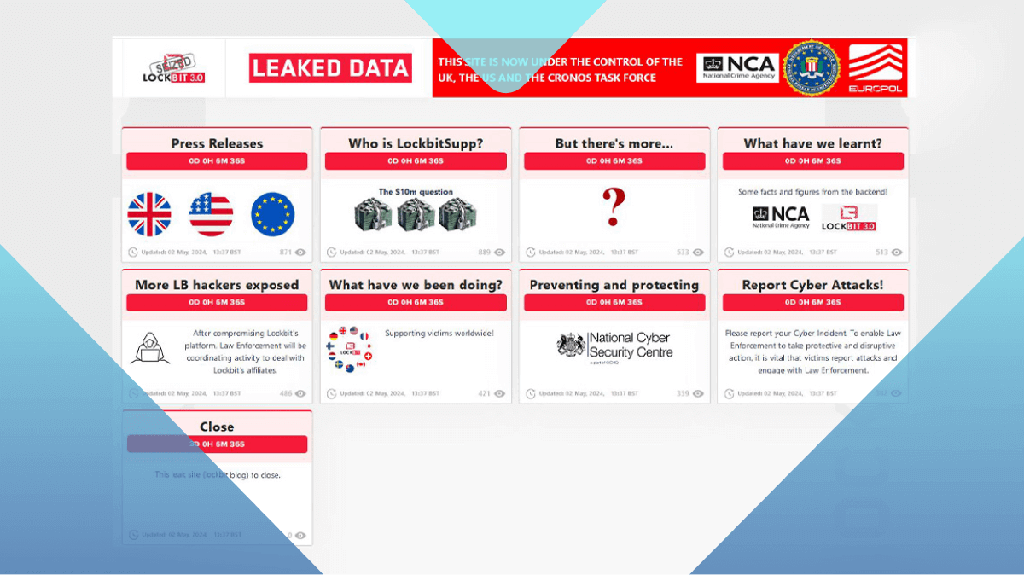
Law enforcement places new teasers on LockBit leak site and reveals
Access a knowledge base on dark web marketplaces, forums, leak sites, and more. Stay updated on privacy breaches, security threats, and expert insights to protect your digital world. Find out if your personal information was compromised in data breaches
Search your email on databreach.com to see where your data was leaked and learn how to protect yourself.
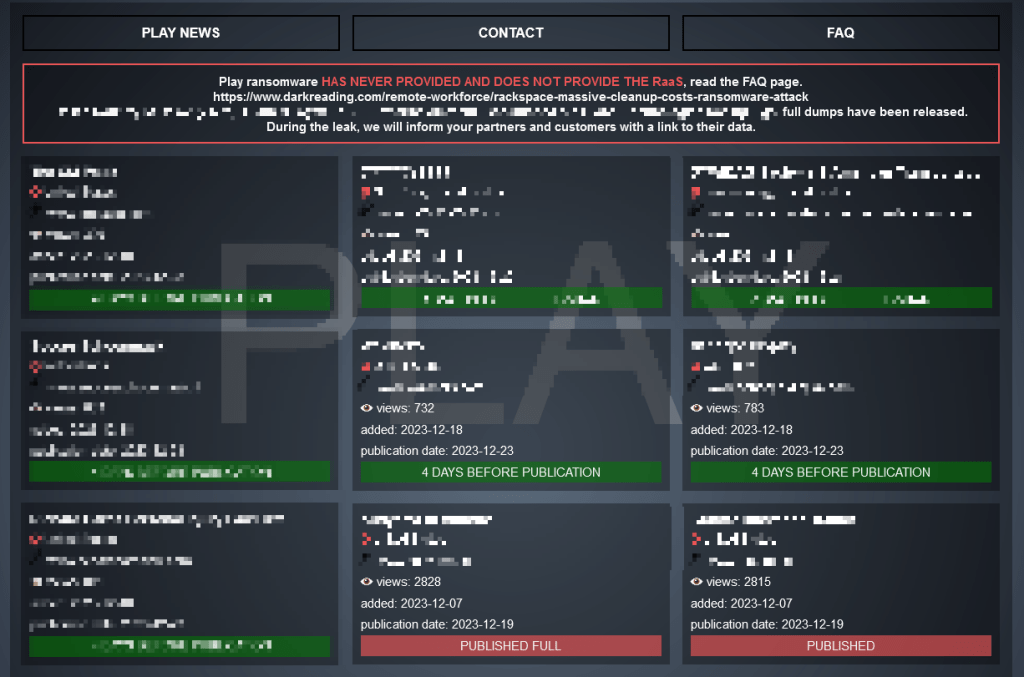
Browserleaks is a suite of tools that offers a range of tests to evaluate the security and privacy of your web browser These tests focus on identifying ways in which websites may leak your real ip address, collect information about your device, and perform a browser fingerprinting. What are dark web leak sites In simple terms, dark web leak sites are criminal bulletin boards
They exist for three main purposes Announcing successful data breaches publishing stolen information to the public extorting victims for ransom payments these sites are often managed by ransomware gangs who treat hacking as a business. A modern personal asset search engine created for security analysts, journalists, security companies, and everyday people to help secure accounts and provide insight on compromised assets Free breach alerts & breach notifications.
Your hub for leaked sensitive data and cyber news