Leaks Web Most Recent Content Files #630
Play Now leaks web VIP broadcast. No subscription fees on our entertainment center. Delve into in a ocean of videos of shows exhibited in superb video, ideal for discerning watching gurus. With the newest drops, you’ll always be informed. Explore leaks web personalized streaming in life-like picture quality for a sensory delight. Register for our creator circle today to get access to exclusive premium content with cost-free, no sign-up needed. Stay tuned for new releases and experience a plethora of groundbreaking original content intended for premium media enthusiasts. Grab your chance to see singular films—start your fast download! Explore the pinnacle of leaks web one-of-a-kind creator videos with crystal-clear detail and special choices.
Browserleaks is a suite of tools that offers a range of tests to evaluate the security and privacy of your web browser Data leak checker we'll check the internet and dark web for your email address or mobile phone number. These tests focus on identifying ways in which websites may leak your real ip address, collect information about your device, and perform a browser fingerprinting.
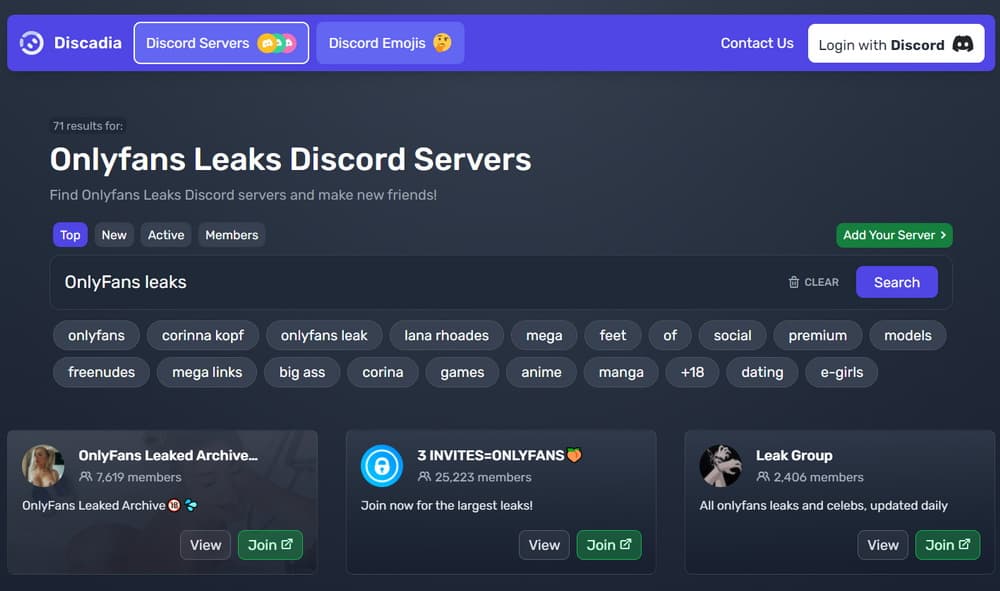
OnlyFans: Creators & Leaks - What You Need To Know Now
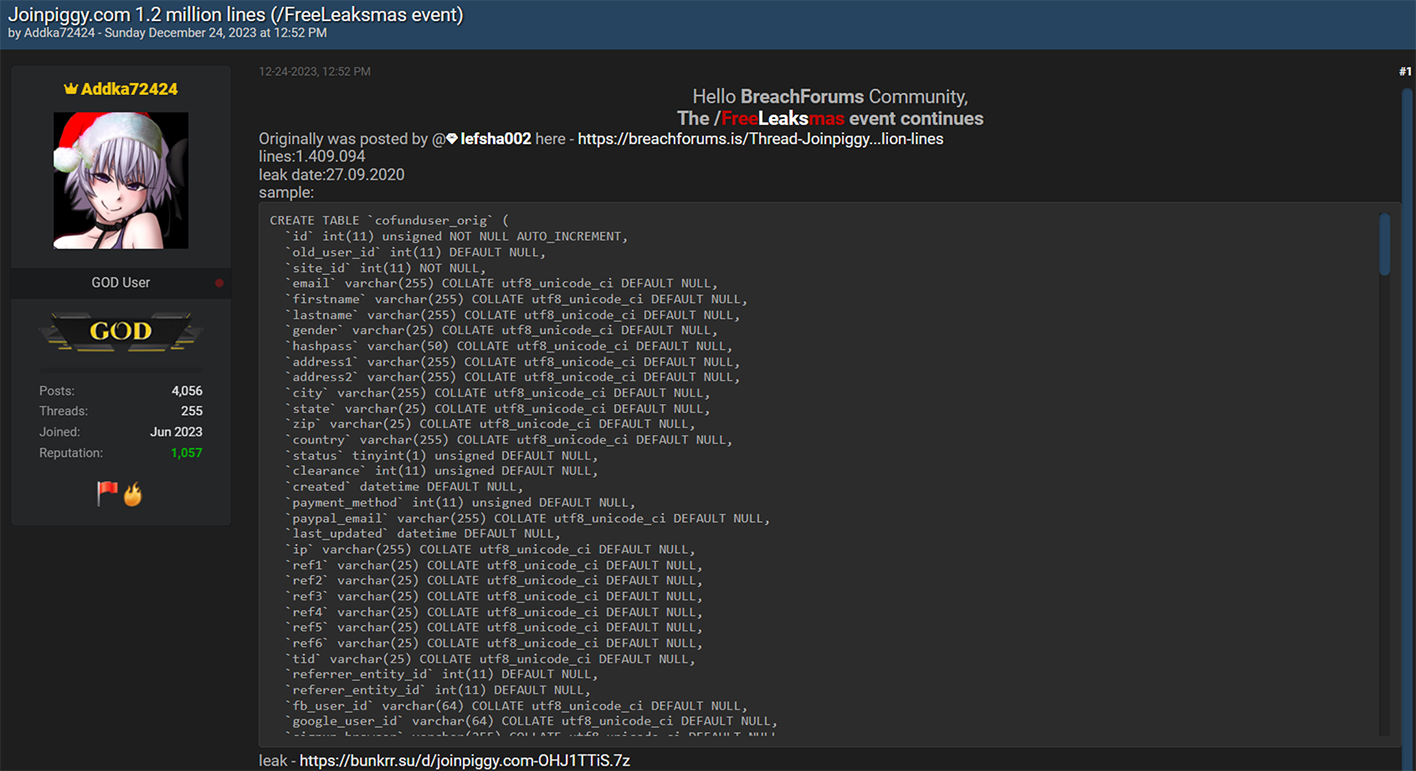
Learn how dark web leak sites occur, how cybercriminals expose stolen data, and the best ransomware prevention practices to protect sensitive information. A web leak refers to the unauthorized release or exposure of sensitive information or data onto the internet, often with unintended consequences Designed for mobile and desktop.
The dark web (sometimes called the darknet) is often romanticized in movies and pop culture, but in reality, it's a very functional part of the criminal underground—a place where cyberattacks are turned into public weapons.
What is a dark web leak site These websites allow threat actors to publish stolen data while preventing law enforcement agencies from easily identifying them. Today, 21 december 2018, wikileaks publishes a searchable database of more than 16,000 procurement requests posted by united states embassies around the world. They take advantage of the web's core principle of composability, which allows websites to interact with each other, and abuse legitimate mechanisms 2 to infer information about the user